How redirecting traffic for inspection works
You can redirect traffic to a proxy service where the traffic can be, for example, scanned for malware before the traffic continues to its final destination.
You can configure a Single Firewall or Firewall Cluster to redirect FTP, SMTP, HTTP, and HTTPS traffic. The main benefit in using the firewall to redirect traffic to a proxy service is that the redirection works transparently: the communicating hosts need no additional proxy configuration when the redirection is done for them at the firewall.
Proxies are typically used for malware scanning and content filtering, but there are more applications. Using an external service allows you to expand the capabilities of the firewall with many other types of content screening. For example, the service can strip certain types of attachments out of emails without blocking the message itself. This type of feature is available directly on the firewall as well, but an external service is a better option in medium to high throughput environments.
For the FTP or SMTP protocols, you cannot use inspection and redirection. You must either redirect the traffic or inspect the traffic locally. You cannot do both.
Figure: Redirection of traffic
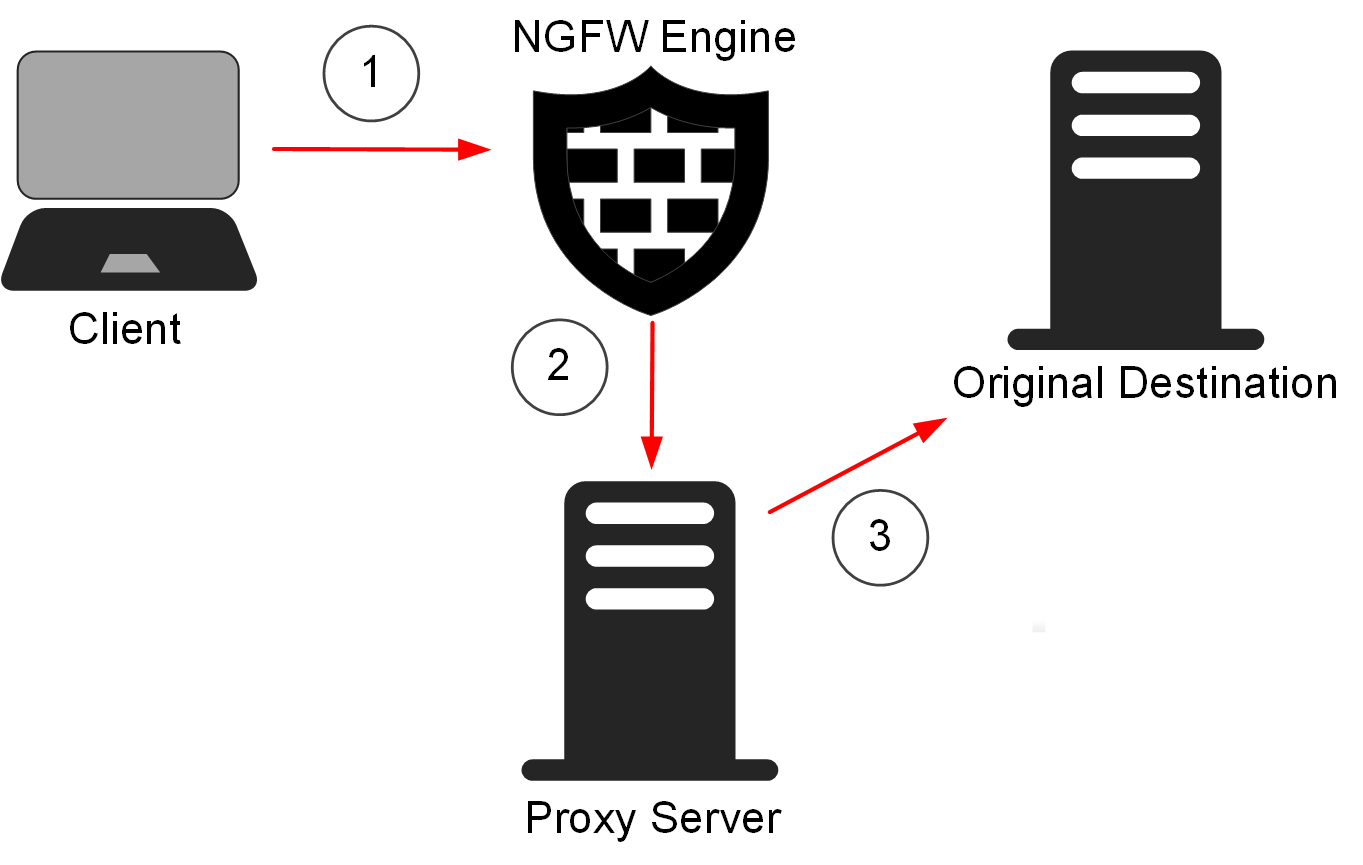
- 1
- Traffic from the client arrives at the NGFW Engine.
- 2
- Access rules in the Firewall policy determine which connections are redirected to the proxy service for inspection.
- 3
- The traffic is inspected and redirected to the original destination.