VPN configuration overview
Many steps might be required to configure a VPN, depending on the complexity of the configuration.
- VPN Gateway elements represent NGFW Engines that are managed by the Management Server (and administrative Domain) you are currently connected to with your Management Client.
- All other gateway devices are represented by External VPN Gateway elements. Forcepoint NGFW Engines that are managed by a different Management Server (or administrative Domain) are also External VPN Gateways.
Due to the various authentication and encryption methods that are supported in VPNs, there are many settings in policy-based VPNs. To prevent repeated configuration work, reusable profiles are used for storing different types of settings. These profiles and other elements related to the configuration of policy-based VPNs are shown in the following illustration, excluding the elements that are related to managing certificates.
Figure: Elements in the VPN configuration (excluding certificate-related elements)
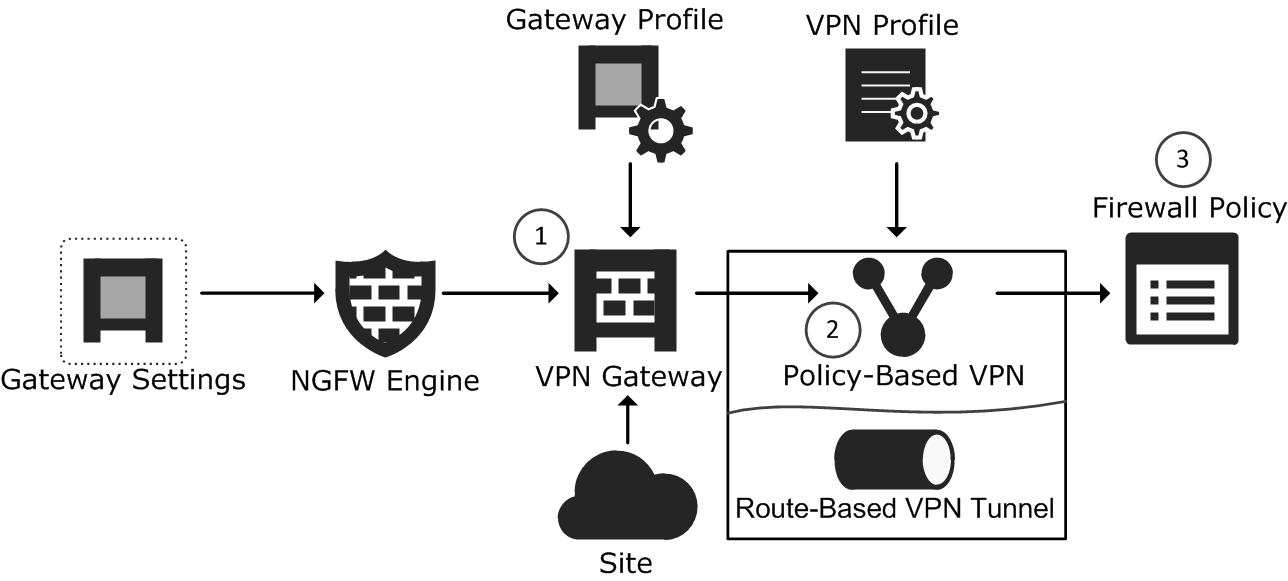
- 1
- The VPN Gateway element represents a Firewall/VPN device in VPNs. One VPN Gateway element is automatically created for each NGFW Engine in the
Firewall/VPN role. You can optionally add more VPN Gateways to the NGFW Engine. Each VPN Gateway element can be used in several
VPNs. The Gateway element refers to the following other elements:
- The NGFW Engine element contains the VPN settings for the VPN Gateway. The NGFW Engine element refers to a Gateway Settings element that defines settings for advanced VPN performance tuning.
- Gateway Profile elements contain information about the capabilities of different gateways, so that the system can disable unsupported options and find incompatible combinations of settings automatically. Gateway Profiles can be created and selected for External VPN Gateways. The Gateway Profiles of VPN Gateways are selected based on the installed software version.
- Site elements define real or translated IP addresses that are routable through the policy-based VPNs. The system can add the IP addresses automatically from routing or you can adjust the sites yourself.
- 2
- The Policy-Based VPN element combines other elements together to define the settings used in one particular policy-based VPN and defines the topology for the VPN.
- 3
- The Firewall Policy controls VPN traffic in the same way as any other traffic.
- The Access rules determine which connections are directed out through each VPN and which traffic is allowed in from each VPN.
- The NAT rules define how address translation is done for VPN connections. The VPN communications between the gateway devices are always subject to NAT as usual. The traffic that uses the tunnels is subject to NAT only if address translation is enabled for the VPN.
Except for endpoint IP addresses, the same elements used in the configuration of policy-based VPNs can also be used when configuring route-based VPNs.
Configuration workflow
- (Optional) If you are configuring a VPN with an external device, you might want to create a custom Gateway Profile specific to the device.
- (External VPN gateways only) Add the necessary number of External VPN Gateway elements to represent the physical VPN devices. External VPN Gateway elements define the VPN endpoints (gateway
IP addresses) and the sites (see the next point). Note: VPN Gateways elements are automatically created for NGFW Engines.
- (Policy-based VPNs only) Configure the sites. Sites define the IP addresses that can be made routable through VPNs. The sites can be adjusted in different VPNs that the gateway establishes.
- (Optional) If the existing VPN Profiles do not have suitable settings for your new VPN, create a custom VPN Profile element. The custom VPN Profile element defines the IPsec settings (authentication, encryption, and integrity checking).
- Define the VPN in one of the following ways:
- Create a Policy-Based VPN element. The Policy-Based VPN element defines the topology (which gateways create tunnels with each other).
- Create Route-Based VPN Tunnel elements to define endpoints for tunnels in route-based VPNs.
- Create certificates, if necessary.
- Add the necessary Access rules according to the type of VPN:
- (Policy-based VPNs) Add the IPv4 Access rules and, if necessary, the IPv4 NAT rules for VPN traffic. Adding rules for policy-based VPNs also activates the VPN on the engines.
- (Route-based VPN) Add Access rules to allow traffic between the internal network and the networks that are reachable through the route-based VPN tunnels.
This workflow contains steps for all kinds of VPN configurations. Alternative next steps are included as necessary to achieve a particular type of configuration. Alternatively, you might want to follow a simplified workflow for building a particular type of VPN.